Security
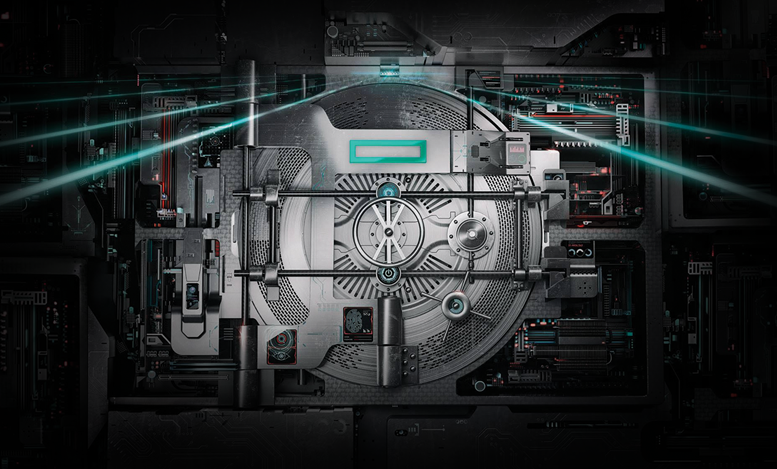
We Need Truly Secure Servers—And HPE Has Them
Spies tied to a foreign government have infiltrated a major server manufacturer and planted tiny microchips on the system boards in order to spy on the American government and its…
Read NowSecure Your Email with Microsoft’s ATP
Sending emails in a corporate world is as natural as breathing. Many times, even I find myself opening an email or hitting send without thinking too much about who could…
Read NowShore Up Your Data Defenses
Over the past year, the headlines have been packed with stories of data center security breaches—there have been high-profile attacks on government agencies, large well-known stores, creditors—the list goes on….
Read NowDo Security Worries Wake You Up at Night?
It’s 3:00 a.m. and your phone rings. Still half-asleep, you fumble for your phone and manage to answer. What comes next are three words that no IT administrator wants to…
Read NowDiscover the Latest Network Monitoring Trends
The last few months have seen many high-profile security breaches brought to light—and now even our Wi-Fi standards aren’t as secure as we once thought. So, how can organizations best…
Read Now