We often read the news and learn of high-profile ransomware attacks on companies and organizations. When we read these stories, many of us think of ransomware attacks as something that only happens to “the other guys.” This is especially true when it comes to smaller organizations, as there seems to be a false narrative that ransomware attacks only affect larger organizations or high-profile companies. However, the reality is that no organization, regardless of size, is ransomware-proof. In fact, when it comes to the current surge in ransomware attacks, it becomes a question of when not if. An organization’s ability to survive an attack depends on their preparedness and ability to minimize damage.
By the Numbers
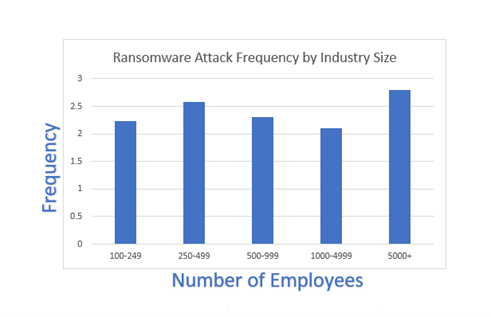
According to latest statistics, ransomware attacks have increased by 62% year-over-year, making this type of attack the most prevalent cybersecurity threat. A 2022 report indicated that a whopping 76% of organizations surveyed were targets of at least one ransomware attack in the last 12 months. In fact, the average ransomware attack frequency was approximately 2.4 attacks in the last 12 months. The size of the organization attacked seems irrelevant as most ransomware attacks are random instead of targeted. The following diagram shows the frequency of ransomware attacks by employee size:
A frightening statistic is that of companies surveyed, over 40% reported data loss and downtime due to a ransomware attack. In various cases, the attack resulted in partial or complete data loss even after a ransom was paid.
When we consider the increasing frequency of ransomware attacks and the high data encryption rate, it becomes clear that an organization’s ability to survive a ransomware attack depends on preparedness and the approach taken to mitigate such attacks. It is no longer enough to prepare for what to do “if we get attacked” but rather to prepare for “when we get attacked.” Preparing for the inevitable or always yields the best results and provides the best damage control options.
Backup Immutability
Being a victim of a ransomware attack is indeed scary and can have an organization-wide impact, but there are various steps that can be taken to minimize damage and reduce the risk of data loss. When it comes to ransomware, it is important to think about prevention; however, it is more critical to focus on mitigation and damage control.
Tip #1: Develop a well-defined contingency plan to help protect your data.
Despite having clearly defined security policies, ransomware attacks are difficult to prevent. As previously mentioned, when we focus on the “when” instead of the “if,” we can develop a well-defined contingency plan to better cope with an attack. One of the best ways to cope with an attack is to minimize the inflicted damage. In most cases, ransomware attacks go unnoticed for days or weeks, and when the attack is identified, it can be too late to prevent data encryption. Therefore, backups play an even more critical role now than they have in the past. We used to think of backups as something that was “nice to have” if we ever needed to recover lost data (a file here, a VM there, etc.). However, backups are now the last line of defense when there is a ransomware attack. It is for this reason that ransomware attacks are increasingly targeting backup images. In the past, backups were not thought of as being part of an organization’s security practices, however, today backups play a crucial role in an organization’s ability to recover from a cybersecurity attack.
One of best solutions available to survive a ransomware attack and minimize damage is backup immutability. When backup immutability is implemented, it prevents backup images from being modified, deleted, or encrypted after they have been written to the backup target. This ensures that if an organization experiences a ransomware attack today, yesterday’s backups are immutable; therefore, they cannot be altered or deleted. Since immutability prevents any modification to the backup images while the immutability period is active, backup images cannot be encrypted by a ransomware attack. This allows for quick data restores to a point in time prior to the attack. Data loss (if any) is limited to the changes that took place from the time the backup image was written to when the attack occurred. This can be further mitigated by establishing clearly defined SLAs and performing more frequent backups.
Immutability: Cloud vs. On-premises
When it comes to immutability, there are some pre-requisites that must be met. First, the backup application must support immutability. Second, the backup target or repository must also support immutability. Immutable backup targets can be located on-premises for quick and fast restores, or they can reside in cloud object storage. The ability to have on-premises immutable storage is highly recommended; however, due to hardware acquisition costs, it may not always be an option. In these cases, immutability on cloud object storage provides an inexpensive way to leverage backup image immutability. If the backup application supports immutability, enabling immutability on cloud object storage is a straightforward process requiring minimal reconfiguration.
On-premises immutability is a bit more complex to deploy, but it does provide some advantages over cloud object storage (i.e., eliminates cloud data transfer costs and increases recoverability speed). However, it tends to be a more expensive solution to deploy due to hardware acquisition costs.
Tip #2: Leverage immutability both on-premises and cloud (preferably both leveraging object storage) as your budget allows.
Given the likelihood of a ransomware attack, backup image immutability should be a critical component of every organization’s data protection and cybersecurity response strategies.
No More Denial—Your Organization Will Be Hit with Ransomware Attacks
When we read that of 3300 organizations surveyed, 76% experienced at least one ransomware attack, it becomes clear that a ransomware attack is likely to occur. Clearly defined security practices help minimize external risk but given the fact that most attacks begin internally through phishing, clickbait, etc., a ransomware attack is almost inevitable. This makes backup immutability one of the best tools available to do damage control and ensure recoverability. Assuming the existing backup application and cloud storage provider support immutability, backup immutability is inexpensive and simple to implement.
Tip #3: Include other security measures such as hardening (operating system and hypervisor) as well as airgap to further contain a ransomware attack and to reduce data loss risk.
While the backup immutability does not reduce the risk of a ransomware attack, it increases an organization’s ability to cope with an attack. It also reduces or eliminates the need to make any ransom payments as encrypted data can easily be recovered. Given how successful and lucrative ransomware attacks are and their increased frequency, thinking that “it will never happen to us” is clearly the wrong approach. The sooner we begin thinking of how to respond to a ransomware attack “when it happens to us,” the better prepared we will be to cope with such an attack.

