Across the global technology theatre, phishing, whaling, and impersonation-based attacks continue to pose substantial risks to organizations around the world. Quite simply, these email attacks utilize social engineering tactics to convince employees to supply critical data. Experienced cyber criminals take full advantage of similarly spelled domain names and/or free email accounts—such as YAHOO and Google—to impersonate outside sales representatives or business leadership. The method of such an attack is one employing “technology camouflage,” where the communication excludes malware links or attachments that are usually included. This approach greatly reduces the likelihood of detection with traditional email security solutions and techniques.

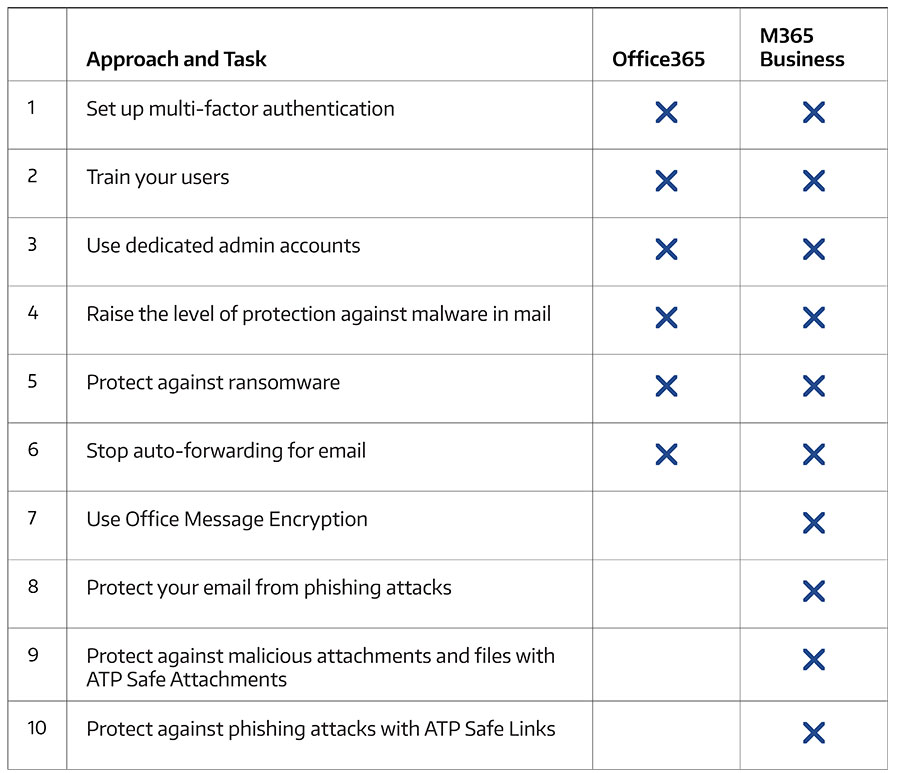
How can organizations leverage Connection Microsoft-based security technologies? For starters, if you are a small- or medium-sized organization using one of Microsoft’s business plans, and your type of organization is targeted by cyber criminals and hackers, Connection can assist your team with increasing the security of your organization by completing the Microsoft-recommended tasks listed in the following table.
There are many key indicators for whaling identifiers within inbound email, such as:
- Is the name of the individual sending the mail the same as one of my user names?
- Is the originating domain sending the email equal or similar to one of my domains?
- Is the sender’s domain new? For example: Has the domain been published and seen on the Internet passing legitimate traffic?
Potentially, your incoming mail may be flagged by multiple forms of protection (for example both EOP and ATP), and multiple detection scans (such as spam and phishing). This is possible because there are ATP anti-phishing policies for ATP customers, and EOP anti-phishing policies for EOP customers. This also means the message may navigate multiple detection scans for malware, phishing, and user-impersonation. Given all this activity, there may be some confusion as to which policy applies.
In general, a policy applied to a message is identified in the X-Forefront-Antispam-Report header in the CAT (Category) property. If you have multiple anti-phishing policies, the one at the highest priority will apply. Microsoft Office 365 provides the ability for your team to apply security policies to counteract the above listed threats. For example, the policies below apply to all organizations:
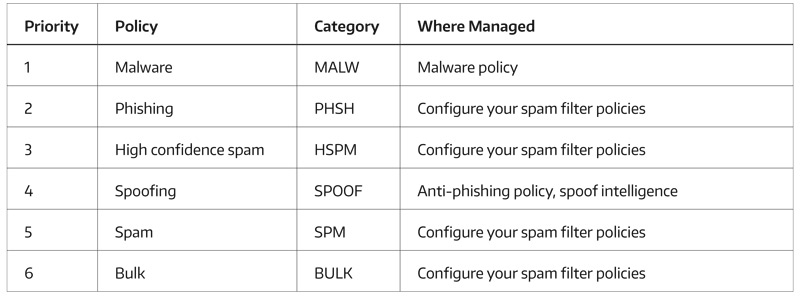
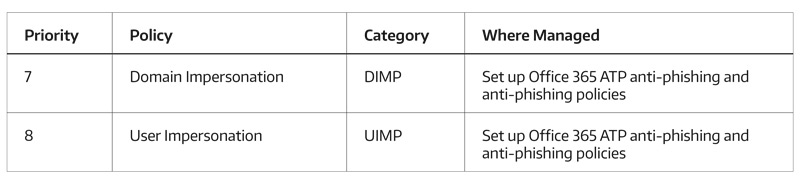
In addition, these policies apply to organizations with ATP.
As an example, if you have two policies with their respective priorities:
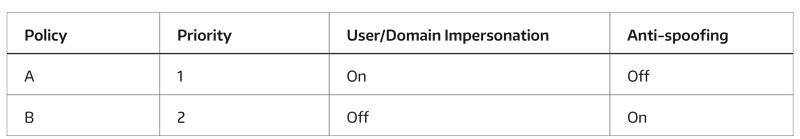
If a message comes in identified as both user impersonation and spoofing (see anti-spoofing in the table above), and the same set of users scoped to policy A is scoped to policy B, then the message is flagged and treated as a spoof. However, no action is applied because though spoof runs at a higher priority (4) than User Impersonation (8), anti-spoofing is turned off.
Keep in mind, administrators can create a prioritized list of policies (see the priority field above), but only one policy will run and apply its actions. That means a user in both policy A and B will have the higher priority policy (A is #1) run, and the message will not filter through any further policies. If the anti-spoofing is off, no actions will be run.
Because there is a potential to have many groups of users in many policies, it may behoove administrators to consider using fewer policies with more capabilities. It is also important to be certain that all users are covered by a comprehensive policy.
Connection works closely with Microsoft to ensure that Office 365 build outs, migration, and delivery services include a variety of threat protection features. Our internal services engineer maintains a comprehensive checklist to make sure your threat protection features are set up for your organization. If you’re new to threat protection features in Office 365, or you’re just not sure where to begin, do not hesitate to reach out to Connection for a FREE Office 365 Security Workshop as part of your successful rollout of cloud-based productivity applications and solutions!


One thought on “The Latest Trends in Phishing and Steps You Can Take to Protect Yourself Today”
Hey there! I’ve been following your site for a while now and finally got the bravery to go ahead and give you a shout out from Porter Tx! Just wanted to say keep up the excellent work!
Comments are closed.