Recently, Facebook announced that a hacker stole login information for 50 million accounts, putting over 90 million users at risk for stolen information. In related news, Uber has reached an agreement to pay all 50 states and the District of Columbia $148 million after their 2016 data breach. “Instead of reporting it, Uber hid evidence of the theft and paid ransom to ensure the data wouldn’t be misused.”
These headlines are no longer a surprise; instead, they have become virtually daily occurrences. What can you do to protect yourself and your organization from data theft?
I grew up in information technology with the old adage of not putting all your eggs in one basket. We are taught that sharing the responsibility between manufacturers reduces single points of failure around a single manufacturer. I frequently tell a story from my hospital days of when I was confronted by an issue that required the assistance of two separate major technology manufacturers; both of which blamed the other, and neither one wanted to speak in front of the other.
When it comes to managing your risks, part of your assessment needs to account for all the different applications, devices, and partners you have involved in protecting your environments and how effective they are working all together. Let’s be really honest about this: Company A might provide an interface to a Company B product, but Company A and B are in direct competition and unlikely to be interested in helping each other make money at their own expense.
To my mind, there are very few companies that provide a security portfolio as large and comprehensive as Cisco combined with their expertise. They should always be in your top three for consideration as a security partner.
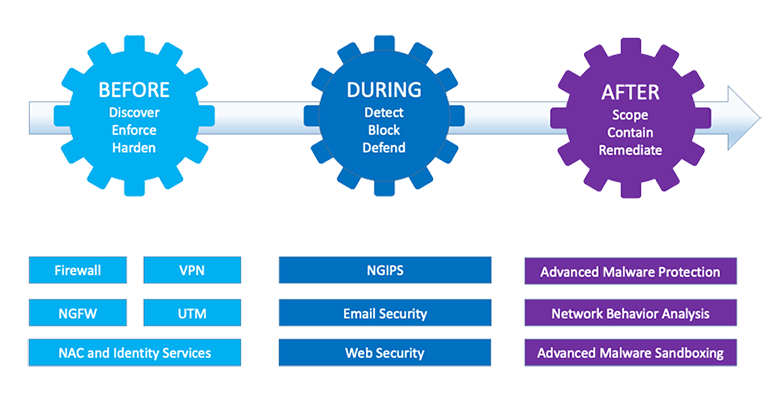
At the foundation of the Cisco security portfolio is the attack continuum security model (pictured below). This is a threat-centric approach to security and provides advanced threat protection, superior visibility, and continuous control before, during, and after an attack.
Attack Continuum
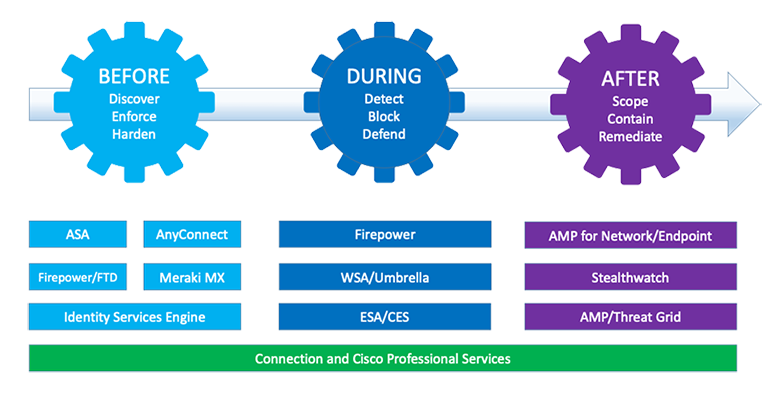
This next diagram shows where some of the portfolio sits along the continuum.
Cisco’s Secure Solutions Provide Comprehensive Threat Visibility and Protection
The recently announced acquisition of Duo Security, specializing in two factor authentication and single sign on services, joins a host of other security acquisitions:
- Sourcefire, an intrusion detection tech firm (2013)—Firepower, AMP, Snort
- Threatgrid, a malware analyzing firm (2014)—AMP
- OpenDNS, a domain name service provider (2015)—Umbrella
- Lancope, a network monitor (2015)—Stealthwatch
Cisco’s commitment to security is unquestionable. Its integration into all areas of our infrastructures provides automation for many normally manual tasks. Catalyst 9k switches feature integrated security so the network can learn and adapt to new threats.
Cisco also provides a service that will assist you during an attack: Cisco Incident Response Service provides you with access to on-site skilled responders with many years of experience dealing with all kinds of incidents. As part of this service, they will also assist you with breach communications so that experts are brought in to help craft the right message.
Take advantage of Cisco’s comprehensive portfolio. If you’re ready to upgrade your security infrastructure, the experts at Connection are ready to help. Give us a call today.

