After the rush to remote that happened in March 2020, most companies have rebounded to be able to quickly move employees to remote or hybrid work as the need arises. Employees can meet with hundreds of participants virtually from anywhere with a strong Internet connection, access work applications from any device, and analyze hundreds of thousands of data points to make better decisions and automate tedious yet critical tasks to save time. Enabling those experiences at scale is the grand vision of the cloud. But the cloud allows that data to be shared across more devices, apps, and endpoints, which increases vulnerability to malicious attacks. How do you keep your data, apps, and infrastructure available to remote workers, while ensuring your organization remains stable and secure?
Delivering the right security for customers’ cloud investments is the most significant challenge that the cloud providers face. To tackle this, companies like Microsoft invest billions of dollars in security research and development. However, cloud security is not just about developing the most sophisticated security tools. The security and privacy principles that govern the proactive evolution of practice frameworks and tools are perhaps the important baseline.
Design Principles for a More Secure Cloud
Microsoft’s approach to designing solutions for the best security entails three things: security that is built-in across devices and platforms, security that is integrated across people and devices and data, and security that is enhanced by AI and automation. This means built-in multifactor authentication, single sign-on, and password-less sign-on for any device that accesses the resources in the cloud. You may also have various purpose-built security tools designed for each use case, such as endpoints, email, clouds, identities, networks, and IoT devices. And it will all be connected and integrated to a centralized system that uses AI and automation to make the detection and remediation easier for humans.
The interconnectedness of Microsoft’s individual security tools is perhaps the most important benefit of Microsoft’s security architecture. It allows the threat signals from each purpose-built security tool to flow to a centralized console like Microsoft 365 Defender and further to Azure Sentinel. Your security analysts will have full visibility of the entire cloud investment.
Related: Strengthen Security and Improve Team Productivity: A Look into Azure Sentinel
Security, privacy, and compliance are closely related, and having a set of principles in place to safeguard the privacy of the company and personal information is a combined effort. When it comes to the privacy of your company and personal information, Microsoft adheres to the following principles:
- Control: This means putting everyone in control of their own privacy with easy-to-use tools and clear choices.
- Transparency: Being transparent about data collection, and how data is being used, so that everyone can make informed decisions.
- Security: Protecting the data that is entrusted to Microsoft through strong security and encryption.
- Strong legal protections: Respecting local privacy laws and fighting for legal protection of users’ privacy as a fundamental human right.
- No content-based targeting: Not using email, chat, files, or other personal content to target advertising.
- Benefit to you: This means collecting data only for the benefit of users, and to make the experience better.
The Importance of the Shared Responsibility Model
Your cloud provider building their solutions upon robust security principles is the first step in providing you the best security, but the responsibility does not end there. According to the shared responsibility model, the responsibility for securing your cloud investments is also upon you. Understanding the shared responsibility model will help you design better security frameworks and practices.
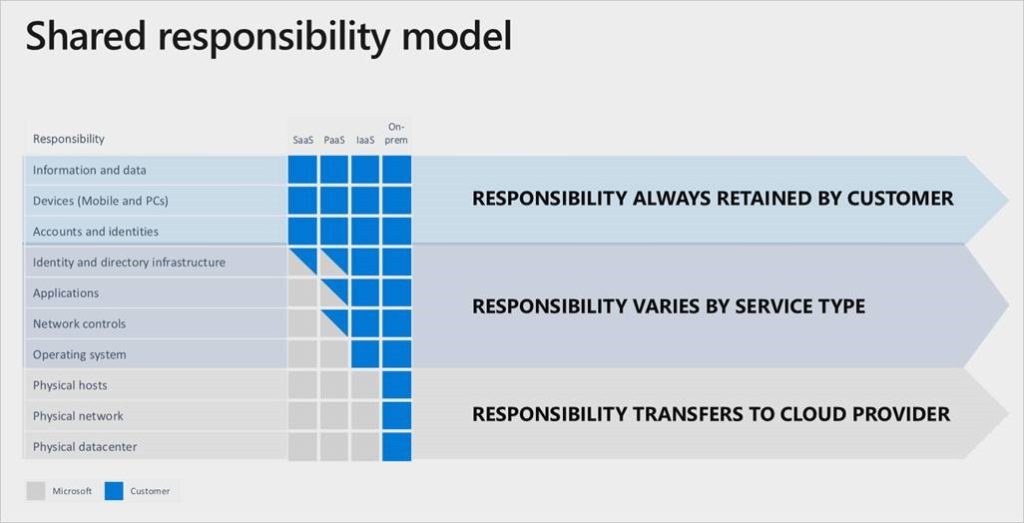
As shown in the picture, the responsibility moves from Microsoft to the customer depending on the cloud service type you choose. While it’s not surprising that the on-premises cloud is fully your responsibility, the fact that you are responsible for the operating system, network controls, and applications on IaaS should not come as a surprise.
The Implications of the Zero Trust Model
The term zero trust was coined by John Kindervag, an industry analyst at Forrester, and now it’s a very popular framework to measure your network security practices. According to the model, you must never trust by default—continuous validation across varied conditions is the only way to trust a user. The zero trust model has resulted in security strategies, such as defense in-depth, that offer maximum protection to your data. Microsoft uses this layered approach in their Azure data centers to protect your data. You can also use this approach to build a security practice for areas in which security is your responsibility.
Wrapping Up
Protecting your data and privacy should not be an afterthought. Through bedrock principles, proactive frameworks, and ever-evolving tools, Microsoft will help you have the best security around your investment. But understanding the shared responsibility models and implementing the right security design principles will ensure that your cloud investments have long-term security. The first step is to plan properly in the initial phase of your cloud journey. Reach out to our Microsoft Security Experts if you need help

