What makes a strong password? Many of us are overly familiar with the standard password guidance of a minimum of 8 characters, a mix of upper and lower case letters, and at least one special character (e.g. @, #, or $). This guidance was provided by the National Institute of Standards and Technology (NIST) in 2003. We also should rotate our password (at a minimum) every 90 days. Many organizations today are enforcing their password policies to follow these “rules.” However, we are starting to see a shift in overall password guidance—so much so that NIST overhauled their guidance in 2017 to encourage the use of passphrases and other authentication methods.
What Is Wrong with Using an Eight-Character Password?
The original guidance from 2003 for password complexity was not bad advice at the time. There needed to be some standards to reference as our digital identities became more prevalent, and many were typically only protected by a username and password. However, the more the original guidance was adopted, the more there were issues with the passwords users would choose. The first is the commonality that ended up being used (P@ssword123, anyone?). By enforcing complex password rules, users had a hard time creating and remembering their passwords. The path of least resistance was taken, and end users made easier-to-remember passwords that met the complexity requirements. The trouble with this is many users, unknowingly to each other, created very similar passwords because we are humans and not complex random password generators. Using common passwords help attackers build dictionaries of passwords that they can automatically check against a username. All an attacker had to do was wait for a successful login to be returned. When it is time to rotate a password, users only make minor tweaks (e.g. P@ssword123$), so they can easily remember their newish password. This is not making the hacker’s job any harder.
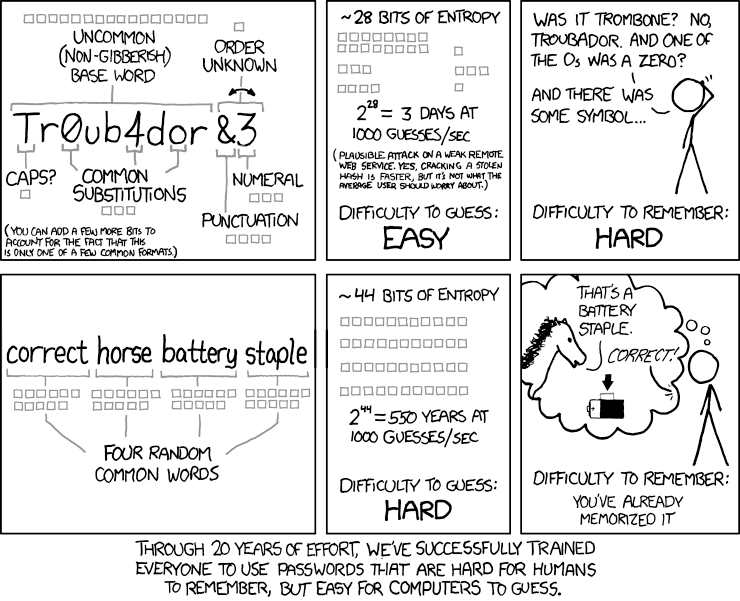
In addition to users unknowingly creating similar passwords, a minimum 8-character password is not very hard to crack for a malicious actor when compared to a passphrase with double the character length. A very interesting read from a Microsoft TechNet article describes how the length of a password is far more important than the traditional password complexity requirements. To summarize: longer passwords have higher bits of entropy, making it very difficult for a hacker to try to guess your unique passphrase.
Enter Stage Right: The Passphrase
By utilizing a passphrase over a traditional password, a user can create a longer password that is easier to remember, and still introduce special characters if necessary. For example, if I create a passphrase with a few of my favorite things, “Copper-Kettles-woolen-mittens-w!ld-geese,” I can create a password that is very easy for me to remember and is exponentially more secure than a traditional password with minimal requirements. When creating a passphrase, you should utilize a handful of words that’s associated, in your mind, to you—and only you. This makes it easy for you to remember and difficult for others to guess. There are such things as bad passphrases too, such as the name of your kids, pets, or favorite foods. These are things that are known to others as well as you. Here are a few dos and don’ts:
- Use a phrase with multiple (4-5) words that are easy for you to remember.
- Use spaces or dashes between the words.
- Use special characters in easy to remember locations/words (if necessary).
- DO NOT re-use passphrases. Create a unique one for each account.
- DO NOT use words or phrases that are easy to identify, or put-togethers (kids’ names, pets, favorite foods, etc.). Think about the content you publish on your social media profiles.
A wonderfully illustrated Web comic from xkcd summarizes a lot of what we covered in this article so far:
What Next?
We should not rely on passphrases or passwords as the end all be all of account protection. They are still stored somewhere on some system. If it’s stored, it can be compromised.
Multi-factor authentication (MFA), or two-factor authentication, is always recommended. It should be used wherever possible to protect your account. By using MFA, your credentials fall into any of these three categories:
• Something you know (like a password)
• Something you have (like a token)
• Something you are (like your fingerprint)
Your credentials must come from two different categories to enhance security. If a malicious actor compromises your password, but cannot generate the second factor, then they will be denied access to your account.
In addition to MFA, I would recommend using a password manager. Password managers are a solution to the issues around creating short, weak, and non-unique passwords. A password manager can randomly generate a long password/passphrase for each account and store it for you securely. This takes the fuss out of creating a password that you have to memorize, creates a unique password for every online account, and puts the questioning to bed on whether the password you created is considered secure enough. A password manager can assist with enhancing many of the fallacies that accompany passwords when left for us users to create and maintain on our own. A few to consider are 1Password, LastPass, or Dashlane. However, a quick search for password managers will turn up a plethora of options and software reviews for the solutions in this space.
Final Thoughts
As we covered, longer passwords are far better than the traditional school of thought (8-character minimum with complexity rules). Use passphrases instead of passwords to make your digital life a little easier to manage while making you more secure all at the same time. However, don’t rely on passwords alone. Do a little research into password managers to help ease the burden of creating and memorizing logins and passwords for the numerous online accounts you may have. And, whenever possible, utilize MFA to increase the security of your accounts.

