What Is Multifactor Authentication (MFA)?
Authentication usually requires a username and password. This is considered single factor authentication. MFA adds another step in the authentication process by requiring a second factor—or some other form of evidence—from the user. This can be a personal identification number (PIN) or the response to a challenge question (something the user knows) or an automatically generated token (something the user has). Multifactor authentication can also use biometric factors (something the user is), such as a fingerprint, facial recognition, or retina scanning. Use of multifactor authentication is popular on mobile devices using soft tokens generated by an app installed, or by SMS messages sent to the user at the time of authentication. It adds a layer of security by combining these different factors, which lowers the risk of compromise—as it would be difficult for an attacker to successfully provide this second factor. Especially if that second factor is sent to your locked phone.
Who Uses Multifactor Authentication and What Are the Benefits?
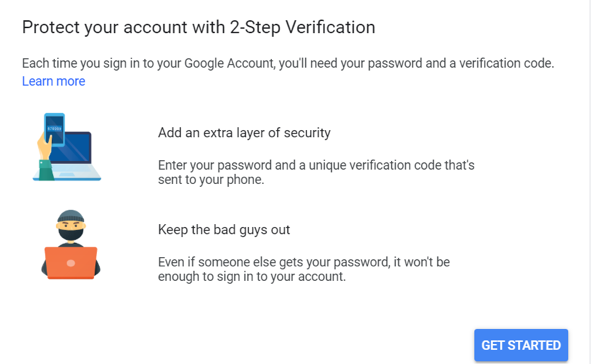
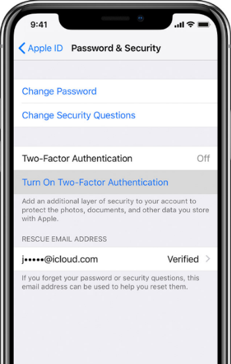
Many companies—such as Google, Twitter, Microsoft, and Apple—are providing support for Multifactor Authentication. Enabling MFA is usually as simple as finding the “Manage privacy settings” menu within an app. It’s also fairly simple to implement. Just keep in mind: every time you log in, you will need to provide that second factor (usually a code texted to your phone), which some people find annoying, even if it does provide additional security. Online services—such as banking and e-commerce—also provide multifactor authentication for users when accessing their services.
Weak and stolen credentials are a leading contributor to breaches. Implementing MFA and discouraging password reuse will help prevent the impact of stolen credentials. Bad actors that steal your password will likely not be able to supply that second factor.
Google’s Authenticator provides easy-to-use MFA.
Facebook allows you set up a one-time passcode (OTP).

You can even enable MFA on an Apple iPhone and in your iCloud.
Even Microsoft Office 365 offers Azure MFA—and Microsoft Windows 10 users can now move beyond centrally stored passwords and leverage FIDO-certified Windows Hello biometrics to access their devices, apps, and online services.
Multifactor in the Enterprise
Multifactor authentication software helps improve the overall security posture across the enterprise—and there is no shortage of MFA vendors to choose from. However, most IT departments are already strapped with projects to help streamline the business. Adding another factor to authentication can tax both IT staff and the user community, so any implementation of MFA should be clearly vetted to ensure a positive user experience.
Universal 2 Factor
Universal 2 Factor or U2F is based on a physical USB key similar to Yubikey. This physical USB key device interacts with the browser on the device to provide an additional layer of security when logging into a protected website. Amazon Web Services support U2F authentication. U2F is developed by Google and Yubico working in partnership and in conjunction with the FIDO2 Alliance and is supported on Google, Android, Firefox, and Opera platforms
Identity theft is an easy, low-risk, high-reward crime and a threat to everyone. Multifactor authentication is one of the most effective ways to help protect against remote attacks and is a market driver for next-generation authentication.

